Attackers are exploiting a Linux Exim critical flaw to execute remote commands, download crypto miners and sniff out other vulnerable servers.
A widespread campaign is exploiting a vulnerability in the Exim mail transport agent (MTA) to gain remote command-execution on victims’ Linux systems. Researchers say that currently more than 3.5 million servers are at risk from the attacks, which are using a wormable exploit.
Specifically under attack is a flaw in Exim-based mail servers, which run almost 57 percent of the internet’s email servers. Attackers are exploiting the flaw, discovered last week, to take control of the victim machines, search the internet for other machines to infect, and to initiate a cryptominer infection.
“These kinds of attacks have big implications for organizations,” said researchers with Cybereason in a post on Thursday. “The recovery process from this type of attack is costly and time-consuming.”
Exim mail servers are open-source MTAs, which essentially receive, route and deliver email messages from local users and remote hosts. Exim is the default MTA included on some Linux systems.
The Flaw
The flaw stems from improper validation of recipient address in the deliver_message() function in the server.
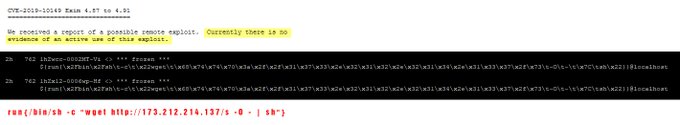
The vulnerability (CVE-2019-10149), which has a critical severity score of 9.8 out of 10 on the CVSS v3 scale, was discovered on June 5 in Exim versions 4.87 to 4.91. Exim version 4.92 is not vulnerable.
“A patch exists already, is being tested, and backported to all versions we released since (and including) 4.87,” according to a recent security advisory. “The severity depends on your configuration. It depends on how close to the standard configuration your Exim runtime configuration is. The closer the better.”
An initial wave of attacks on this vulnerability – which involved attackers pushing out exploits from a malicious command-and-control (C2) server – was first discovered June 9 by researcher Freddie Leeman.
“Just detected the first attempts to exploit recent #exim remote command execution (RCE) security flaw (CVE-2019-10149),” he said in a tweet. “Tries to downloads a script located at http://173.212.214.137/s (careful). If you run Exim, make sure it’s up-to-date.”
Then more recently, researchers with Cybereason tracked a second wave of attacks which they believe are launched by a different attacker.
The Worm Attack
The more recent and sophisticated campaign first installs an RSA private authentication key on the vulnerable SSH server for root authentication. Once remote command-execution is established, the attacker then deploys a port scanner, to sniff out other vulnerable servers and installs a coin-miner.
In addition, the campaign appears to be “highly pervasive” with extra measures – such as installing several payloads at different stages including the port scanner and coin-miner – for persistence on the infected system.
“It is clear that the attackers went to great lengths to try to hide the intentions of their newly-created worm,” researchers said. “They used hidden services on the TOR network to host their payloads and created deceiving windows i con files [which is actually a password protected zip archive containing the coin miner executable] in an attempt to throw off researchers and even system administrators who are looking at their logs.”
con files [which is actually a password protected zip archive containing the coin miner executable] in an attempt to throw off researchers and even system administrators who are looking at their logs.”
Researchers said that they are still looking for further information about the attack, but in the meantime urged users to patch every Exim installation in their organization and make sure that it is updated to the most recent version, Exim version 4.92.
“The prevalence of vulnerable Exim servers (3,683,029 across the globe according to Shodan) allows attackers to compromise many servers in a relatively short period of time, as well as generate a nice stream of cryptocurrency revenue,” researchers said.
via threatpost.com