When he was just 16, Jonah made hundreds of thousands of dollars ripping off some of the world’s biggest tech companies. A self-described social engineering expert, he boasts that he could steal practically anything with just a laptop and a cellphone. He made a small fortune on an online black market. He vacationed in Switzerland, toured Paris and Rome, and crashed in luxurious Las Vegas suites, always under an assumed identity. His family and friends wouldn’t see or hear from him for years at a time.
“I made thousands, money whenever I needed it,” he boasts. “I could social engineer anything. Anything I wanted.”
Now in his early 20s, Jonah—not his real name, of course—works at a private security firm, protecting the same companies he once robbed. On the condition of anonymity, he agreed to talk about the methods he once used as a criminal.
Part theater and part science, social engineering is the method by which hackers, for lack of a better term, exploit vulnerabilities in human psychology; for Jonah, it was a key to getting anything he wanted, from televisions and laptops to smartphones and expensive wines. One of his largest takes netted him around $60,000 worth of product, he says. He showed me a Rolex Daytona watch—part of a gallery of stolen goods he’d photographed in his bedroom—which retails on Amazon for around $26,000.
Whether through face-to-face interaction, by phone, or by email, the human gatekeepers of any network can be exploited—if you know how to play the game. They’re the weakest link in any company’s security.
Almost every major electronics company is vulnerable in nearly the same way: They all have warranty-based replacement systems that can be exploited. Most companies, for instance, don’t require a defective item to be returned before mailing out its replacement. It’s likewise difficult to prove that an in-warranty item has been lost or stolen.
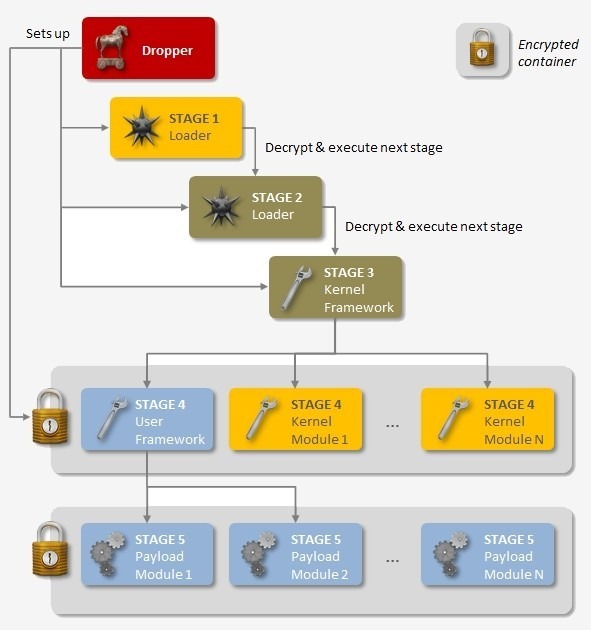
Through repeated phone calls, social engineers develop strategies for navigating a company’s customer help line. They get a feel for which sob stories and which “yes” or “no” responses will work best toward achieving their objective. Intelligence, temperament, and even humor all come into play. The questions and responses are then mapped out, as if composing a flowchart, with the goal of expediting the con.
Part theater and part science, social engineering is the method by which hackers, for lack of a better term, exploit vulnerabilities in human psychology.
By ensuring that products can be easily replaced, in the interest of good customer service, these companies have created—perhaps unavoidably—gaping flaws in their own security.
“All the big companies—Apple, Microsoft, Razor, HP, Sony, Phillips, Casio, Rolex, Samsung—they’re all vulnerable to warranty exploitation,” Jonah says.
At this very moment, the world’s top tech manufacturers are unwittingly shipping hundreds upon thousands of dollars in free merchandise all over the world to people like Jonah. Most of them, he says, are teenagers with too much time and not enough supervision. This scam, which relies heavily on a universally flawed warranty system, has been streamlined by hackers with a high degree of technical sophistication. Now almost anyone can do it—and thousands of people are, every day.
“The problem is pretty big,” Jonah says. “There’s a lot of people doing it. It costs nothing to provide no security, so the companies just ignore it.”
 A social engineer shows off his “massive 7-day haul” on a “bragging rights” forum.
A social engineer shows off his “massive 7-day haul” on a “bragging rights” forum.
According to Jamie Woodruff, the chief technology officer at Patch Penguin, a London-based cybersecurity firm, hundreds of social engineering websites exist, dedicated to the types of scams Jonah describes. “There are numerous invite-only sites online where you can learn how to rip off companies like Amazon,” he says. “Everything you need, from the method, to stolen PayPal accounts and credit cards, can be either purchased or traded for.”
In his free time, Woodruff monitors social engineering websites, studying the black markets where techniques are bought and sold. He says Amazon is one of the more vulnerable companies, because comparatively, it requires very little effort to steal an Amazon account, which can then be squeezed for all it’s worth.
“I started learning and putting my own ideas into it, my own twists on the companies and the exploits.”
“I’ve talked Amazon into resetting people’s passwords with only three pieces of information: a name, home address, and an email address,” Woodruff says. “The thing is, customer support is there to help people and make it easy for their customers, but in the end they’re making it easier for hackers as well.”
After weeks of fishing for an invite, I gained access to socialengineered.net, a social engineering forum where PayPal and Amazon accounts are bought and sold for $10 or less. It was on a private forum like this one, called AstroPID, that Jonah learned how to acquire everything he wanted but couldn’t afford. There, in 2011, users exchanged tips on how to use social engineering on customer service agents. The site has since been shut down.

At the forum I’m on now, on a page titled “Methods,” users freely offered advice on how to steal a wide variety of merchandise, from Keurig coffeemakers to iPads, Lenovo laptops, Canon DSLR cameras, Armani clothes, and even free McDonald’s cheeseburgers.
In one such post, a user provides detailed instructions on how to scam Intel out of free computer parts by claiming that the product arrived with the security seal intact, but the box was visibly empty through the plastic packaging. “If you are lucky, they will offer a refund straight away,” the user wrote.
 Users exchange methods for social engineering Steam, Apple, Intel, Microsoft, and more.
Users exchange methods for social engineering Steam, Apple, Intel, Microsoft, and more.
In retrospect, Jonah’s first scam was almost too easy.
The first step, he said, was to collect as many product serial numbers as possible. Initially, he did this in person, nervously wandering through Wal-Mart with a pen and a piece of paper, jotting down the numbers imprinted on the backs of TVs, laptops, and gaming consoles. Once he returned home, Jonah would call up a customer service agent at Microsoft or Phillips or Hewlett Packard, and he’d read directly from a script posted on AstroPID. Within in a few minutes, the agent on the end of the line agreed to mail him a “replacement” for a device that was still sitting on a shelf at Wal-Mart.
Often, the customer service agent would ask for a credit card that could be charged if Jonah failed to mail the malfunctioning device back to the company. This wasn’t much of a hurdle. He would purchase gift cards at the grocery store, which he then used to buy virtual credit cards online using an alias. He was astounded to learn that almost every company he called accepted the digital cards as a retainer.
“If they follow a script, for instance, I know they’re a low-level employee or recently hired. And they’re the types of employees we can exploit.”
“You can type ‘virtual credit card’ into Google and find one that doesn’t require you to give up any personal information,” Woodruff says. “You can load the cards with just a few bucks. Apple and Microsoft, for instance, will authenticate them—and they’ll pass a quick check—but they won’t actually charge them for 30 days, or after they don’t receive the item they’ve replaced.”
Initially, Jonah had the companies mail the products to a nearby house, one that was recently put up for sale and had no ties to his real identity. The first few times, he was nervous about showing up to collect the packages, but he soon realized that no one was waiting there to catch him; there were no surveillance teams in vans around the corner.
 Steps 1-4 (out of 8) for acquiring a free Logitech HD Pro Webcam C920 on a social-engineering forum.
Steps 1-4 (out of 8) for acquiring a free Logitech HD Pro Webcam C920 on a social-engineering forum.
He eventually quit school. The corners of his room were lined with stacks of unopened packages. Hocking them for cash was the tricky part, but he soon discovered a way around that, too. Using an alias, he began placing ads online for unused TVs and laptops at $500, $800, and $1,500 a pop. When someone made a purchase, he’d work the same con as before, but he’d cut himself out of the picture entirely—allegedly having companies mail the “replacement” devices directly to the buyers.
“You wouldn’t believe, there are hundreds of thousands of people doing this,” Jonah says, “but the way they do it is by following someone else’s guide. I started learning and putting my own ideas into it, my own twists on the companies and the exploits.”
Skilled at math and programming, Jonah devised that many companies relied on static algorithms to generate product serial codes. Once he cracked a formula, he claims he could write his own program to generate in-warranty serial numbers. It was the revelation that significantly lowered both his risk and the amount of time between shipments. Such serial code generators are easy to come by on today’s black markets.

A modern serial code generator
Jonah had also begun writing his own phone scripts, which he updated constantly and shared with no one. “When you use the same trick over and over, or too many other people get a hold of it, the technique becomes saturated,” he says. Basically, the company catches on and tweaks its return policy accordingly.
These methods and scripts are the currency of black markets—what’s bartered by scammers looking for new ways to cheat the system.
“Everyone has their own methods, and they buy methods and sell methods. Even I have methods no one knows about,” Woodruff notes. He discovered, for instance, that there are countless “lost and found” websites—many are run by major airports—where electronics, such as iPads, are listed by serial number. Apple’s own website has a support page for checking the warranty status of devices by serial number.
“You can’t secure everything all of the time. There’s just no patch for ignorance.”
I listened in on a three-way phone call while Woodruff demonstrated how this feature could be exploited for a free iPhone. “I don’t know the IMEI code,” he told Apple customer support, “but I do have the serial number.” He pretended to be stupid, as if he couldn’t figure how to turn the damn thing on. “When you call someone up, it’s about being one of two things: You’re either very assertive and very straight to the point, or you act like a complete idiot,” he told me later. “If you act like you’re completely incompetent, they get pissed off and give it to you anyway.”
Woodruff’s invisible phone, of course, wasn’t registered in his name. Before he could get a replacement, the Apple ID had to be changed. “My grandfather bought it for me on eBay, I think,” he told Apple. “But he passed away recently and I don’t have a receipt.” Instantly, the agent told him “no problem,” and proceeded to change the name of the phone’s owner in his system.
That’s when Woodruff terminated the call.
 At a conference, Woodruff discusses using a Domino’s Pizza uniform to social engineer his way past corporate security.
At a conference, Woodruff discusses using a Domino’s Pizza uniform to social engineer his way past corporate security.
It’s not hard to identify the type of employee who would likely fall for this trick, he says. “If they follow a script, for instance, I know they’re a low-level employee or recently hired. And they’re the types of employees we can exploit, because they don’t know the rules, they don’t know the policies, and they don’t know the procedures.”
The problem, according to Woodruff, is that these systems are set up to be very simple to navigate. Companies like Apple have to account for customers who are essentially technologically illiterate. The only way for companies to protect themselves would be a massive overhaul of their procedures, which may not be cost-effective. “This may be chalked up as the cost of business,” he says. “Unfortunately, it’s also affecting their customers. If I were a criminal, I could have easily stolen someone else’s phone just now.”
Until companies like Amazon and Apple start taking into consideration their losses and the ways in which hackers and social engineers target their customers, Woodruff adds, they won’t bother implementing better security.
For major companies, it’s not whether they’ll get ripped off but when. “You can’t secure everything all of the time,” Woodruff says, “There’s just no patch for ignorance.”
Eventually, however, the risks do start to outweigh the rewards. For Jonah, that breaking point occurred when he was backpacking through Europe a few years ago. He started to suspect that someone he’d ripped off was hunting for him. He wouldn’t say what he stole, but he was in Italy at the time. He called a friend to pick him up at the airport in his home country, and the next day he got rid of the merchandise still piled up in his house.
“I was going to get caught eventually,” he says. “You can’t get away with it forever.”
Photos by JVCAmerica/Flickr (CC BY 2.0), Yutaka Tsutano/Flickr (CC BY SA 2.0), John Karakatsanis/Flickr (CC BY SA 2.0), Luke Ma/Flickr (CC BY 2.0), Kārlis Dambrāns/Flickr (CC BY 2.0) | Remix by Jason Reed
via kernelmag.dailydot.com