In a presentation at Black Hat security conference in Las Vegas last week, Kaspersky security experts Vitaly Kamluk and Sergey Belov, along with Anibal Sacco from Cubica Labs, demonstrated how legitimate software Computrace, which is part of the BIOS firmware, can be used as “an advanced removal-resistant BIOS-based backdoor.”
The software, developed by Absolute Software and embedded in BIOS PCI Options ROM and UEFI firmware, has remote code execution capabilities by design and its purpose is to offer computer owners the possibility of remote management of the devices.
However, because it does not encrypt communication with the server, it can be hijacked, if an attacker gains control over the network traffic (man-in-the-middle attack) of the affected computer.
Computrace runs through two agents identified as “rpcnetp.exe” (Small Agent) and “rpcnet.exe” (Main Agent), and as Kaspersky researchers have discovered, on some systems it is enabled by default, making the machine susceptible to compromise.
Vitaly Kamluk says that they do not believe that a malicious reason is behind the component being active without user consent. Instead, they think that manufacturers have it turned on unintentionally.
But, regardless of the reason, the component presents a risk to users on whose machines it is enabled.
The researchers found that two types of remote attacks can be conducted against Absolute Computrace, one directed at the Small Agent module and the other at the Main Agent.
“It’s important to note that Small Agent runs for a limited time starting from initial installation of the module and ending when the system is connected to the Internet and module is successfully updated,” say the experts in the whitepaper detailing the flaw.
In the second type of attack, the Main Agent is pushed to replace the Small Agent.
At the beginning of the communication, no encryption is available for the protocol, but it seems that this is added at a later stage. However, cybercriminals are offered a window to take advantage of the non-encrypted protocol to gain control over the system.
Because the software is not malicious and is developed by a trusted entity, most antivirus products have it whitelisted.
The first glitch was discovered at the beginning of the year and reported Absolute Software at that time, but according to the presentation slides from the conference, had no reaction.
The second remote code execution vulnerability, reported on June 25, generated a response from the company, who denied its existence.
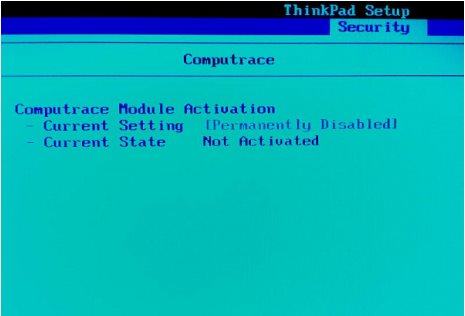
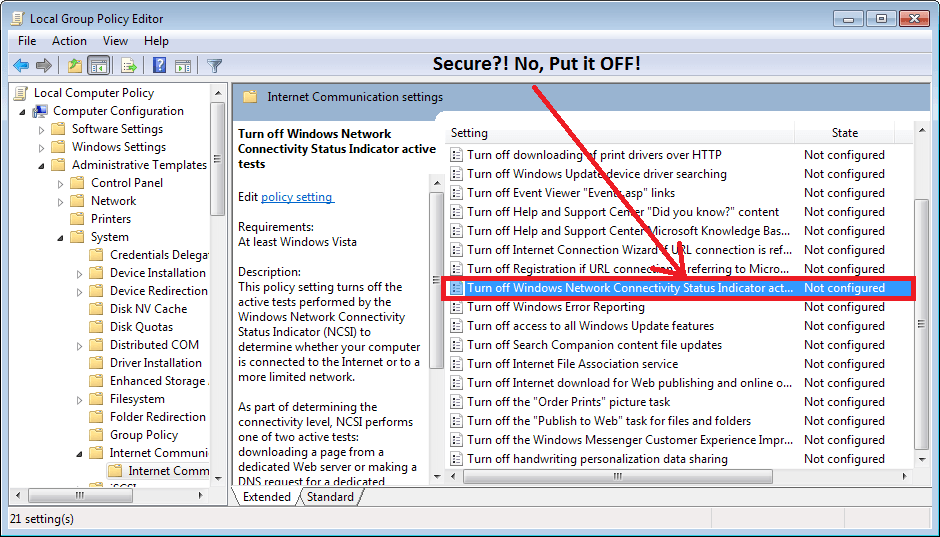
Computrace presence is revealed by the executables of the two agents in the list of processes as well as by connection to certain hosts. Disabling it, however, is more difficult because it is a vendor specific process, and the developer of the BIOS setup utility decides whether to include the possibility to turn on or off the Computrace module.
via news.softpedia.com