Researchers at the Fujitsu Security Operations Center spotted a strain of Dyre being served exploiting hundreds of compromised home routers.
According to the popular security expert Brian Krebs, criminals are exploiting a new technique to spread the Dyre banking malware, they are leveraging hacked wireless routers.
Dyre is usually downloaded by the malicious trojan Upatre, it is a powerful malware capable to perform man-in-the-middle attacks through browser injections and harvest the victim’s credential.
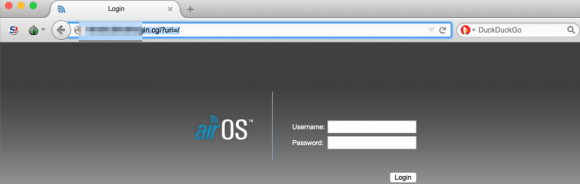
Recently, security researchers at the Fujitsu Security Operations Center in Warrington (UK) spotted a strain of Upatre being served from hundreds of compromised home routers. The experts noticed that the cyber criminal mainly exploited MikroTik and Ubiquiti’s AirOS routers.
“We have seen literally hundreds of wireless access points, and routers connected in relation to this botnet, usually AirOS,” said Bryan Campbell, lead threat intelligence analyst at Fujitsu. “The consistency in which the botnet is communicating with compromised routers in relation to both distribution and communication leads us to believe known vulnerabilities are being exploited in the firmware which allows this to occur.”
Experts speculate that attackers have compromised so many routers by exploiting devices with default credentials (e.g., “ubnt” for both username and password on most Ubiquiti AirOS routers). The experts noticed that many devices used to spread the Dyre malware had the Telnet port wide open.
Brian Krebs highlighted that it isn’t the first time that botnet of routers were used by hackers for illegal activities, according to the investigator the popular hacking crew LizardSquad used a number of compromised home routers to run DDoS attacks that brought down the Microsoft’s Xbox and Sony Playstation’s networks.
It is important to change factory settings for any device to avoid that bad actors exploit default administrative credentials for routers and other network devices to control them.
Websites like routerpasswords.com provide default administrative credentials for several different models of routers produced by various manufacturers.
via securityaffairs.co